Keeping a tab on your SSL certificates is a crucial part of a sysadmin's job.
There are various ways to do it. You can use a monitoring service like Checkmk to monitor the certificates or you can use the good old openssl command for this purpose.
In this guide, I'll explain to you how to use the openssl command to check various certificates on Linux systems.
Optional: Generating a TLS/SSL Certificate
To demonstrate this guide, I'll create some keys and certificate files. If you already have these things, you can skip to the next step.
Let's begin with a private key, use the following command to create a private key:
openssl genrsa -out my_private_key.key 2048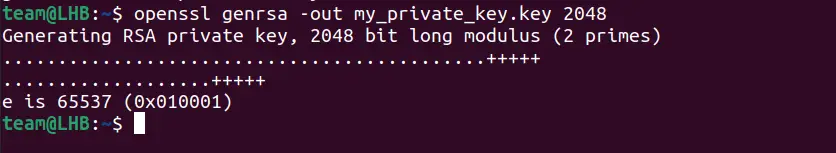
The above command will create a key with the name my_private_key.key file.
Now that you have a private key, create a public key with it:
openssl rsa -in my_private_key.key -pubout > my_public_key.pub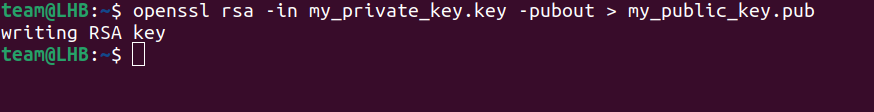
That's good, you now have your private and public keys and you can use them to generate a certificate file. It is important to know beforehand that you are generating a self-signed certificate here. This is because using a CA (Certificate Authority) for signing a certificate requires additional costs.
But don’t worry. Your certificate will suffice as you will use it only for demonstration purposes. Use the below command to build your certificate:
openssl req -x509 -new -key my_private_key.key -days 365 -out mycert.pemThe above command will result in a PEM-type certificate file with the name mycert.pem.
Each option here has its meaning. The 365 indicates the period in days for which the certificate will be valid.
Now enter the details for various questions on the prompt:
Country Name (2 letter code) [AU]:IN
State or Province Name (full name) [Some-State]: [Name of your state]
Locality Name (eg, city) []: [Name of your city]
Organization Name (eg, company) [Internet Widgits Pty Ltd]: [Name of your organization]
Organizational Unit Name (eg, section) []:
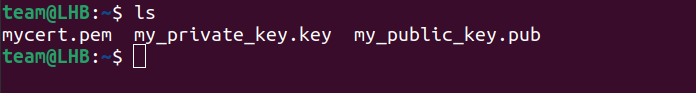
Common Name (e.g. server FQDN or YOUR name) []:[Enter a common name here]You can now see all your files listed in the current directory with the ls command:
Checking the Status of a Certificate
It is very important to ensure the SSL certificates you are using are not expired or on the verge of being expired. Negligence in this regard can have a devastating impact on the production systems.
Certificate files usually have a .pem or .crt extension. You can use the openssl commands to explore the details of a certificate. For example, the below command gives the details of the certificate you created above:
openssl x509 -in mycert.pem -text -noout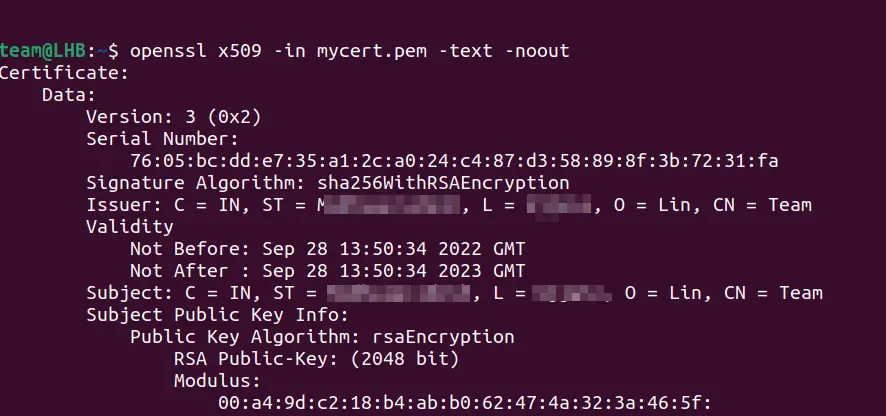
You will see a long output printed on your terminal describing various attributes of the certificate as: Version, Serial Number, Signature Algorithm, Issuer, Validity Status, etc.
Similarly, you can use this command with a port with an SSL certificate attached to it. I guess you will have figured out the validity range of our certificate from the above output.
Always use this command when you plan to replace or renew your SSL certificate. This way you are likely to avoid any mistakes in certificate management.
Using OpenSSL to View the Status of a Website’s Certificate
Let me show you how you can use openssl command to verify and check SSL certificate validity for this websitewww.linuxhandbook.com or a remote system with a fully qualified domain name (FQDN):
openssl s_client -connect linuxhandbook.com:443 2>/dev/null | openssl x509 -noout -dates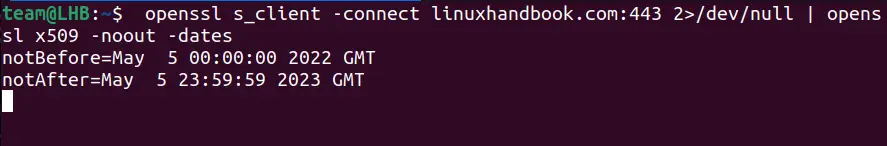
As you can see from the output, the target certificate is valid only for the specified range: May 5, 2022 to May 5, 2023.
Let’s break down this command:
- s_client: This command implements a general SSL/TLS-based client and establishes an SSL/TLS connection to a remote system.
- -connect host:port: Here, you specify the host and port number to connect to.
- x509: This command has multiple uses like showing certificate-related information, converting certificates to various other forms, signing certificate requests, etc.

Verifying Information within a Certificate
CER and CRT type files can be used in parallel as both are identical. The openssl command can also be used to verify a Certificate and CSR(Certificate Signing Request).
Verifying a .crt Type Certificate
For verifying a crt type certificate and to get the details about signing authority, expiration date, etc., use the command:
openssl x509 -in certificate.crt -text -nooutChecking a .csr (Certificate Signing Request) type file
You can use the below command to check a csr type file and retrieve the CSR data entered while creating this file:
openssl req -text -noout -verify -in server.csrVerifying a KEY type file
This is an extra tip for verifying a KEY type file and its consistency:
openssl rsa -in my_private_key.key -checkWorking with .pem type Files
In a mega IT setup, you may find thousands of servers out there. They only accept certificates that are formatted in a particular manner. This means if you are using a .pem format for a server that needs .crt format, then you are at a complete loss until you convert them to the desired format.
Technically, there are some commands that you can use to convert certificates and keys to other formats. In this way, you can make them work with different types of formats required by various servers. For e.g., you can convert a DER file (.cer, .crt or .der) to PEM format as:
openssl x509 -inform der -in base-certificate.cer -out target-certificate.pemTo find the expiration date of a .pem type TLS/SSL certificate, the following command is very handy:
openssl x509 -enddate -noout -in /path/of/the/pem/fileVerifying a Public Key
The public key contained in a private key and a certificate must be the same. You can check this with the openssl command as:
openssl x509 -in certificate.pem -noout -pubkeyopenssl rsa -in ssl.key -pubout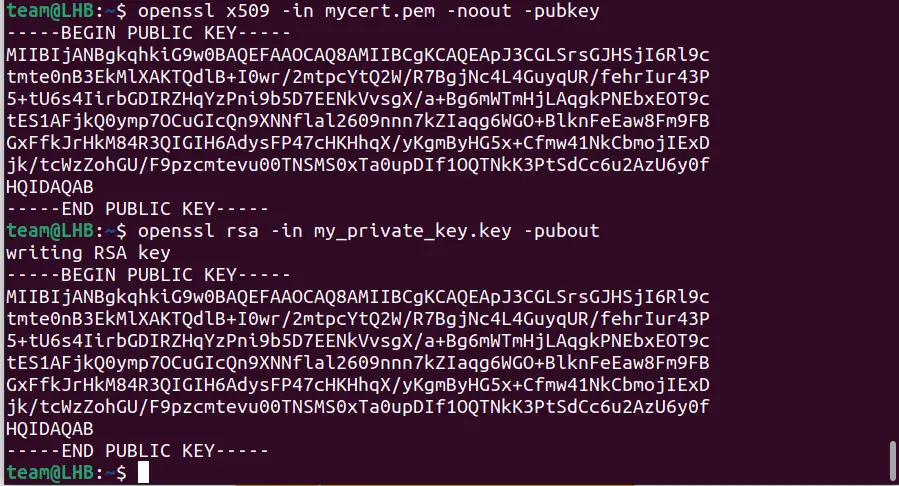
As you can see, the outputs from the above commands are the same.

Conclusion
You have so far seen how to generate keys and certificates, how to change one form to another, and how to verify different types of files.
Keeping knowledge of your certificate status is very important and OpenSSL does a good job here. Also, if you do not want to engage (or mess up) with the command line, you can use downtime monitoring services like Better Uptime to automatically check the certificates.